Is vulnerability management the answer to keep the security risks at bay?

How vulnerability management has taken over traditional methods to safeguard the firms
January 21, 2021
Why vulnerability assessment should be an integral part of an IT system
February 12, 2021Vulnerability management provides different risk ratings and scores for different vulnerabilities, helping the firms eliminate major risks first up, before dealing with smaller vulnerabilities
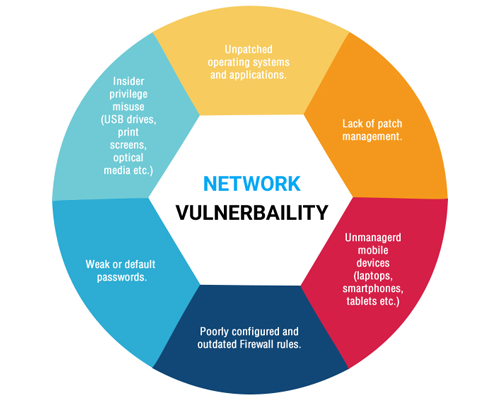
A vulnerability management solution comprises of several options, including vulnerability scanning. It is capable of probing several identified systems for different attributes, which include an operating system, open portals, installed software, user account, etc.
In order to associate known vulnerabilities to the scanned systems, a database is exploited by vulnerability scanners. If some of the systems behave erratically, these scanners can disrupt the networks and systems or exclude them from vulnerability scans. An enterprise can also schedule them to run during off-hours for certain reasons.
A vulnerability scanner scans a new system when it connects to a network. After that, the identified risks are evaluated. Vulnerability management provides different risk ratings and scores for different vulnerabilities. It helps the enterprises to eliminate the major risks first up, before dealing with smaller vulnerabilities. However, it is important to understand the true risks posed by a vulnerability to look beyond the false positives.
Once a vulnerability is evaluated, it is time to treat it. There are many ways to treat them and one of them is remediation. Through this process, one can fix or patch a vulnerability to avoid exploitation. Other than this, mitigation can also lessen the impact of a vulnerability, especially when it is not possible to fix it.
An enterprise can also leave a vulnerability in its original state, if the cost of fixing the same is more than the cost incurred due to it, which is called acceptance. The firm can understand the efficiency of its vulnerability management program using different options for exporting and visualizing vulnerability scan data. The IT system of an organization can apply the remediation technique appropriately, as per the nature of the vulnerability.