How vulnerability management plays a vital role in mitigating possible threats

Vulnerability scanning: Why does your organization need it?
July 16, 2020
How vulnerability assessment helps in averting security threats?
August 29, 2020The process of identifying, evaluating, treating and reporting on security vulnerabilities in systems and the software that runs on them is called vulnerability assessment. Web infrastructure security companies like WebSecure can automate this process for the clients by identifying, evaluating, treating and reporting vulnerabilities:
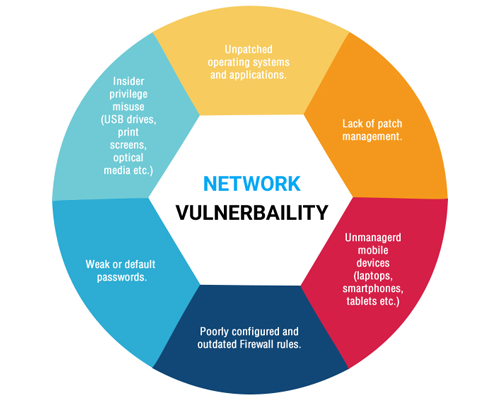
Identifying Vulnerabilities: A vulnerability scanner is what takes the lead in vulnerability management solution. It is able to identify a variety of systems running on a network, such as laptops, virtual and physical servers, databases, firewalls, switches, printers, etc. Then the identified systems are probed for different attributes, including operating system, open portals, installed software, user accounts, file system structure, and more.
The vulnerability scanners use vulnerability database to associate known vulnerabilities to the scanned systems. At times, these scanners can disrupt the networks and systems or exclude them from vulnerability scans if some systems behave erratically. They can also be scheduled to run during off hours, if the available networks bandwidth becomes limited.
When a new system connects to a network, it is scanned by a vulnerability scanner as soon as possible. However, the scanners aren’t the only source to gather system vulnerability data.
Evaluating Vulnerabilities: In order to deal with the identified risks appropriately, the vulnerabilities are evaluated. Different risk rating and scores for vulnerabilities are provided by the vulnerability management, which are helpful for the organizations to decide which of the vulnerabilities should be dealt with first up.
However, the true risk posed by any given vulnerability depends on some other factors beyond ratings and scores. Performing vulnerability validation can help weed out false positives for the organizations to focus on dealing with the real thing.
Treating vulnerabilities: After deeming a vulnerability as a risk, the next step is to prioritize how to treat that vulnerability with original stakeholder to the business or network. Vulnerabilities can be treated in different ways that include:
Remediation: This process includes fixing or patching a vulnerability so that it can’t be exploited. Organizations strive for such ideal treatment options.
Mitigation: It is about lessening the impact of a vulnerability, which is sometimes necessary when it is not possible to fix the same. This option is used to buy time for a firm to remediate a vulnerability.
Acceptance: This is justified when a vulnerability is deemed to be at a low risk and the cost of fixing a vulnerability is greater than the cost incurred. Remediation can be as simple as applying a readily available software patch.
Reporting vulnerabilities: Regular vulnerability assessment enables organizations to understand the efficiency of their vulnerability management program. There are different options for exporting and visualizing vulnerability scan data. It helps IT teams understand which remediation technique will help fix most vulnerable with less effort.